Please NOTE This will be a REMOTE meeting ONLY.
Topic & Speaker 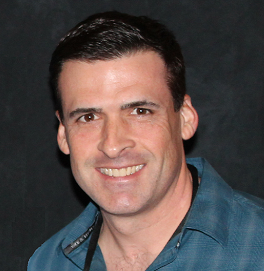
Glenn Howard
Understanding the CISSP domains and the CBK
Abstract
If you intend to climb the career ladder in IT or Cybersecurity, you should consider being certified by ISC(2). The most popular and respected certifications is of course, the Certified Information Systems Security Professionals (CISSP). The CISSP certification validates your skills and experience as an information security practitioner for your organization.
Many organizations including the U.S. Government, rely on this exam to ensure the readiness of their IT security teams and because CISSP is globally recognized and is one of the most sought-after certifications in information security, it is listed as one of the top security certifications you should seek out.
The current Common Body of Knowledge (CBK) is made up of 8 domains and you will need to be proficient in each domain to receive and maintain your certification. In this month's presentation, I will break down each of the eight domains from the CISSP CBK, including how much weight each domain holds in the exam and their relevance to your day-to-day operations.
Speaker's Biography
Glenn Howard is the Technical Program Manager and Senior DevSecOps Engineer with Accenture Federal Services – National Security Portfolio (Formerly, Novetta), in San Antonio, Texas. He designs and builds features for implementation in production systems and operational employment using technologies like Ansible, Terraform, Kubernetes, and Docker. He proactively resolves technical hurdles and continues innovative efforts within an Agile SAFe development practice and collaborates with other team members to decompose large tasks into small testable tasks.
He is also a retired Air Force veteran who served in various leadership roles at the squadron, detachment, brigade, joint special operations and numbered Air Force levels. He holds a Masters of Science in Cybersecurity & Penetration Testing and the following professional certifications: CISSP, RHCSA, CNSSI, AWS Certified Solutions Architect and Joint Cyber Training Environment (JCTE) Engineer.
Glenn is also an adjunct professor of Cybersecurity at the University of Madison, Wisconsin, and Saint Mary’s University, where he instructs & mentors students on Cybersecurity concepts to include: Cloud-Security, Network-Security, Linux-Security, Windows Security and More.
Glenn was elected to be the President of the San Antonio Chapter of ISC(2) which supports thousands of cybersecurity and IT practitioners in one of the largest cyber-hubs 2nd only to Washington DC.
He has an extensive background in IT, DevOps, cybersecurity, national level intelligence and cyber operations and has conducted offensive and defensive cyber operations around the world.
Meeting Agenda
-
Chapter Business - 12:00 - 12:15
-
Speaker time - 12:15 - 1:00
-
Q & A & Networking - 1:00 - 1:30
Continuing Professional Education (CPE) Credit
The membership chairperson will submit one or more CPEs for this event for (ISC)²® members. Please bring your (ISC)²® membership number to the meeting. Attendees will also receive an attendance receipt via email from the Chapter's Board members to support his or her continuing education requirements.
